Как зарегистрироваться на БК Леон
Леон (Leon) – букмекерская контора России, за регистрацию в которой дают приветственный бонус. Чтобы увеличить сумму вознаграждения, введите промокод BMTOP при открытии счета (обязательно ознакомьтесь с условиями предоставления бонуса до внесения депозита).
Леон – легальный российский букмекер, поэтому после регистрации счета требуется идентификация (если не проходили процедуру в других БК). На официальном сайте leon ru и в мобильных приложениях доступна регистрация иностранных граждан, но нужен номер телефона, начинающийся с префикса +7 (нужно быть готовыми к нюансам по идентификации). Здесь узнаете, как Леон БК скачать на смартфон.
Продолжительность регистрации – до 1 часа. Т.е. 5-10 минут нужно на заполнение формы и получение кодов в SMS, столько же на отправку запроса для идентификации и такое же время на проверку загруженных сведений и документов. Если проходили идентификацию в одной из БК, входящих в Единый ЦУПИС, то регистрация в Leon пройдет быстрее: нужно указать только данные для входа в аккаунт.
Что нужно для регистрации
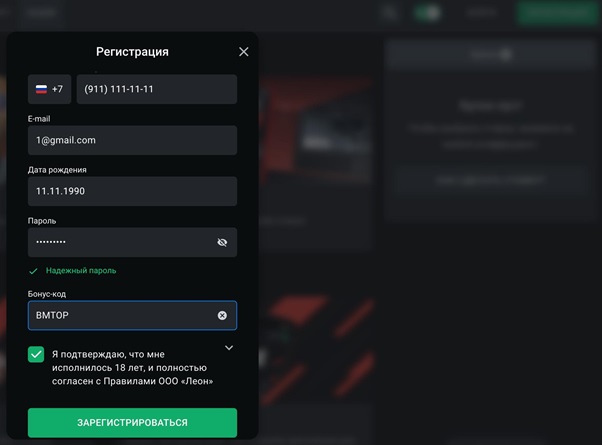
После клика на зеленую кнопку «Регистрация», расположенную в правом верхнем углу, пользователь видит форму для открытия счета:
- телефон (автоматически подтягивается префикс +7, который нельзя изменить – для регистрации счета в Леоне нужен российский номер);
- email (на почту присылают уведомления об акциях, бонусах и т.д., кидают информационные сообщения);
- дату рождения (проверка возраста, т.к. к ставкам на спорт допускаются лица старше 18 лет);
- пароль (комбинация, которая будет использоваться с логином для входа в личный кабинет);
- бонус-код (по умолчанию ячейка свернута, но необходимо нажать на нее и открыть поле для ввода промокода).
При регистрации учетной записи игрок подтверждает, что ознакомлен и согласен с правилами, политикой конфиденциальности, обработки данных, договором и т.д. Система не пропустит на следующий этап, пока не нажмете галочку.
Регистрационная форма защищена при помощи reCAPTCHA (против ботов, DDOS-атак и т.д.).
После клика на зеленую кнопку «Зарегистрироваться» букмекерская контора Леон показывает информационное сообщение о том, что нужно подтвердить номер мобильного. Если в других БК отправляют смс-сообщение, то в Leon звонят. Поднимать трубку не нужно! Достаточно ввести последние 4 цифры номера.
Если прошло больше 5 минут, а для подтверждения аккаунта звонок не поступает, можно запросить его повторно.
После завершения регистрации букмекерская контора показывает уведомление со статусом идентификации. К примеру, появляется сообщение: «По данным системы QIWI, для номера [здесь указывается номер, на который открывали счет] не пройдена идентификация. Чтобы начать игру, подтвердите личность. Это займет не больше 5 минут». Т.е. БК уведомляет, что игрок должен идентифицироваться для заключения пари и использования аккаунта.
Что дает регистрация в Leon
Леон (Leon) – букмекерская контора, известная бонусной политикой. БК устраивает акции с раздачей фрибетов, зачислениями на депозит и др. Внедрена программа лояльности с начислением очков и переводом в рубли. Чтобы забрать фрибеты или заработать очки, делают ставки с пополненного и идентифицированного аккаунта. Лимиты по суммам в месяц зависят от статуса идентификации: онлайн (упрощенная) или оффлайн (полная).
После регистрации счета можно управлять балансом, писать в техподдержку (Леон – контора, где чат с онлайн-консультантом открывается только после авторизации), получать и использовать бонусы, делать ставки и т.д.
Верификация
Как и в других легальных конторах, в Леоне внедрена идентификация после регистрации (если не проходили процедуру до этого). Вторичная идентификация Леон возможна при изменении паспортных данных.
Также БК вправе запросить персональные данные, если подозревает игрока в мошенничестве, мультиаккаунтинге или использовании других «нежелательных для букмекера» стратегий, отмыве денег и т.д.
Оранжевая кнопка «Пройти идентификацию» будет в личном кабинете.
После клика на нее пользователь видит форму с выбором удобного способа идентификации (упрощенная):
- через сайт leon.ru или мобильные приложения – нужно вписать данные паспорта (бесплатно);
- через «Госуслуги» – при наличии подтвержденного аккаунта на gosuslugi.ru (бесплатно).
Пошаговую инструкцию, как идентифицировать аккаунт в букмекерской конторе Леон, вы найдете в отдельной статье.
Чтобы верифицироваться быстрее, нужно загрузить только запрошенные фото документов в том формате, как указывает БК. Проверка после отправки документов на идентификацию занимает не больше часа (зависит от загруженности службы безопасности). Пользователь получает уведомление на email.
Если отправили фотографии, прождали больше суток, а статус верификации в личном кабинете Леона «Проверка не пройдена», для активации пишите в техподдержку.
Что делать, если не получается зарегистрироваться в Леоне
Написать письмо на адрес электронной почты (самого e-mail на сайте Леона в «Помощи» нет: нужно выбрать раздел с техподдержкой и заполнить форму обратной связи). Почта — help@leon.ru — находится в разделе «Контакты».
Консультант онлайн доступен после авторизации в личном кабинете.
Актуальный телефон горячей линии Леон не представляет.
«Сегодня ночью на Крымском мосту произошло чрезвычайное происшествие, очевидно, спровоцированное украинскими националистами.
Зеркала выглядят точно как оригинальный сайт и имеют те же функции. Вам не потребуется заново регистрироваться на сайте-зеркале, все клиентские данные переносятся и на новый сайт. В том числе и сумма на вашем аккаунте. Пользоваться таким сайтом легально, ведь доступ к нему не заблокирован.
Можно в лайве или прематче и на любой вид спорта. Участвуют ставки от 300 рублей.
5 марта 2016, 10:00 Автор Sports.ru
Для получения единовременного бонуса до 3999 рублей клиенту необходимо пройти регистрацию, идентификацию и произвести первый депозит. Сумма бонуса равна сумме внесенных денег. Деньги с бонусного счёта поступают на игровой после того, как игрок заработает необходимое количество леонов.
Организуем доставку товара в 51 регион России и готовы свести к минимуму дефицит товарных остатков на складе партнера. Компании, торгующие под брендом Флекси, располагают тремя логистическими центрами (Москва, Курск и Пенза) и собственной транспортной компанией. Гарантируем, что приобретенный ассортимент сантехнического оборудования прибудет в торговую точку в срок. Сантехника и трубопроводная арматура на нашем складе в полном наличии и не зависит от условий сезона.
43% опрошенных Mediascope сочли рекламу букмекеров наиболее запоминающейся.
Чтобы отыграть фрибет от букмекера Leon, пользователь делает одиночную ставку с коэффициентом выше 1.70. По видам спорта ограничений нет. Отсутствуют условия по прематчу или лайву, а также конкретным рынкам.
Акция доступна только для новых игроков.
Данная форма не предназначена для приёма обращений граждан в порядке Федерального закона от 02.05.2006 № 59-ФЗ «О порядке рассмотрения обращений граждан Российской Федерации» и предоставляет возможность направить электронное сообщение в рамках реализации пилотного проекта по внедрению «Единого окна цифровой обратной связи». Ответ на сообщение будет направлен не позднее 8 рабочих дней после дня его регистрации, а по отдельным тематикам – в укороченные сроки.
Вместе c Леон Comm Зеркало ищут:
- Бк Леон Без Идентификации
- Леон Букмекерская Контора Как Вывести Деньги
- Леон Букмекерская Контора Линия
- Leon Бк Вход
- Бк Леон Отзывы 2023
- Промо Бк Леон